Security Controls Traceability Matrix Template
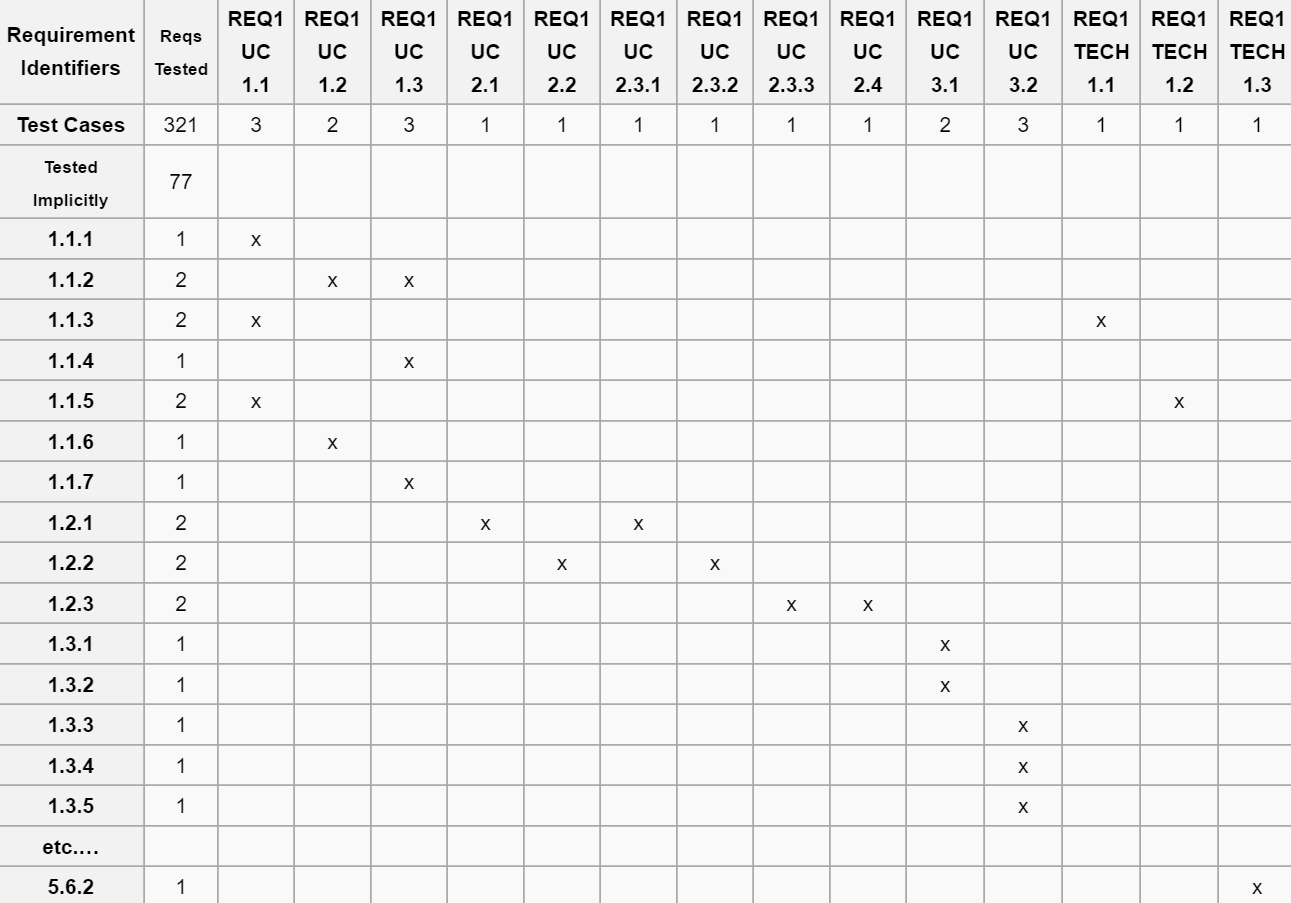
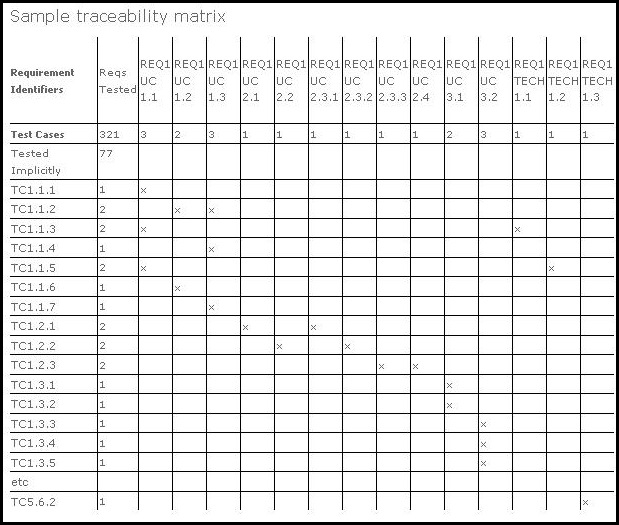
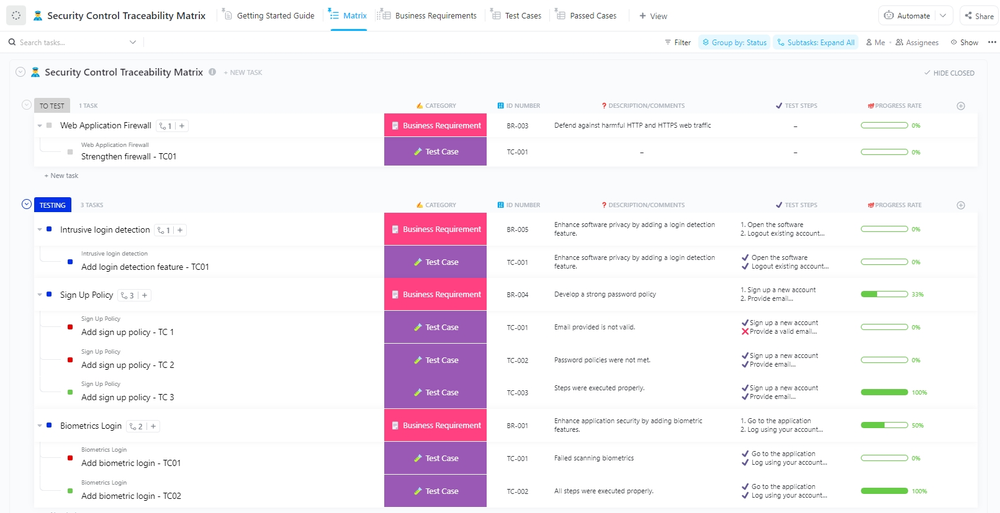
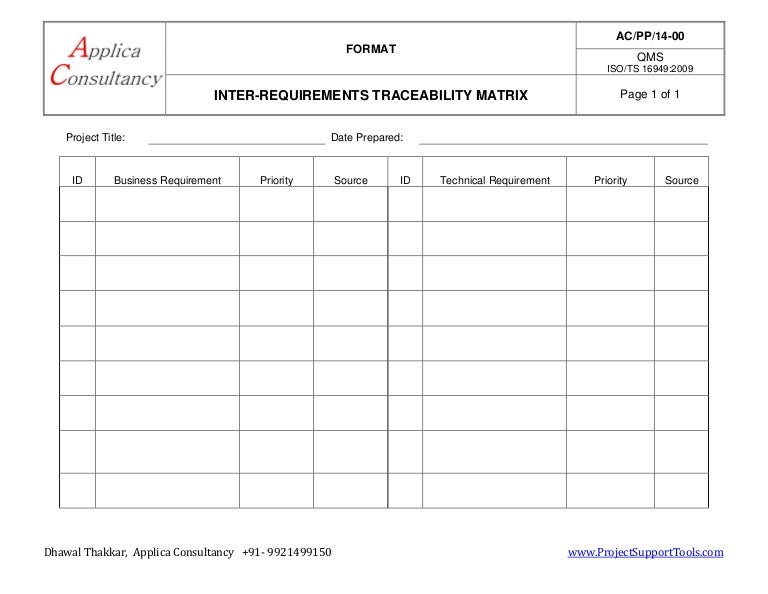
Security Controls Traceability Matrix Template - Web requirement traceability matrix (scope) | complete guide to rtm. Web security requirements traceability matrix (srtm) matrix documenting the system’s agreed upon security requirements derived from all sources, the security features’ implementation details and schedule, and the resources required for assessment. Now the excel sheet is to be created and each artifact should be added in different columns. To keep the traceability matrix operational and workable, avoid unnecessary documentation. This column should contain the id of any associated utilities used for requirements tracking such as a repository, pipeline document, etc. Web the requirements traceability matrix (rtm) relates requirements from requirement source documents to the security certification process. Could also be called security requirements. Web how to use a security control traceability matrix template 1. This is where you'll determine what you want to trace and why, and collect the necessary documents. •considerations include whether the system is a general support system, major application, or a minor application. This column should be populated with a description of the software module(s) linked to the functional requirement. Serious about security & privacy. This helps ensure that no functionality is overlooked during software testing. To keep the traceability matrix operational and workable, avoid unnecessary documentation. The first step is to identify all of the security controls that will be included in. Also, remove expiry documents from links and citations. Web requirements traceability matrix associated id(s): To keep the traceability matrix operational and workable, avoid unnecessary documentation. This helpful ensure that no functionality is overlooked during software testing. 4) addition of the facts. Web requirement traceability matrix (scope) | complete guide to rtm. This column should be populated with a description of the software module(s) linked to the functional requirement. The first step to build a requirements traceability matrix is to create the template, or shell, of your matrix. Web requirements traceability matrix (rtm) docx: This is where you'll determine what you want. This helps ensure that no functionality is overlooked during software testing. Identify all of the requirements needed for the project, including any processes, tasks, goals, and milestones. Web here are 6 steps for using the traceability matrix template to track the progress of a project: Web eplc template version : Web the security control product matrix template quote a framework. Web security controls for a security requirements traceability matrix (srtm). Srtms are necessary in technical projects that call for security to be included. Highest levels of uptime the last 12 months. Web security requirements traceability matrix (srtm) matrix documenting the system’s agreed upon security requirements derived from all sources, the security features’ implementation details and schedule, and the resources required. This column should be populated with a description of the software module(s) linked to the functional requirement. A unique id number used to identify the requirement in the requirement traceability log. This is where you'll determine what you want to trace and why, and collect the necessary documents. Web here are 6 steps for using the traceability matrix template to. Web eplc template version : •considerations include whether the system is a general support system, major application, or a minor application. The first step to build a requirements traceability matrix is to create the template, or shell, of your matrix. Web create a requirements traceability matrix template. Audience the principal audience for this guide includes individuals responsible for designing, managing,. The first step is to identify all of the security controls that will be included in the. Through this new approach, pm/isos may avoid. Here is the link to the aws one. Arrange columns or fields in a way that has a clear depiction and comprehensibility. Web a security requirements traceability matrix (srtm) is a grid that allows documentation and. It ensures that all security requirements are identified and investigated. This column should contain the id of any associated utilities used for requirements tracking such as a repository, pipeline document, etc. Web security requirements traceability matrix (srtm) matrix documenting the system’s agreed upon security requirements derived from all sources, the security features’ implementation details and schedule, and the resources required. Web security controls for a security requirements traceability matrix (srtm). Web requirements traceability matrix (rtm) docx: It ensures that all security requirements are identified and investigated. Web here are 6 steps for using the traceability matrix template to track the progress of a project: Free forever with 100mb storage. Web here are 6 steps for using the traceability matrix template to track the progress of a project: Now the excel sheet is to be created and each artifact should be added in different columns. Once you’ve identified the security controls, you will need to. Free forever with 100mb storage. A unique id number used to identify the traceability item in the requirements traceability matrix. •additionally, determinations are made as to whether the system is web based, along with other srtm factors. This column should contain the id of any associated utilities used for requirements tracking such as a repository, pipeline document, etc. Web security controls for a security requirements traceability matrix (srtm). Highest levels of uptime the last 12 months. It is, therefore, a correlation statement of a system’s security features and compliance methods for each security requirement. Srtms are necessary in technical projects that call for security to be included. 4) addition of the facts. This helpful ensure that no functionality is overlooked during software testing. Through this new approach, pm/isos may avoid. Web create a requirements traceability matrix template. Web the security control verify matrix model offers a scope to confirm that suggested security requirements are examined through test cases. A unique id number used to identify the traceability item in the requirements traceability matrix. Each row of the matrix identifies a specific requirement and provides the details of how it was tested or analyzed and the results. Maintain only one traceability matrix for a project. Identify all of the requirements needed for the project, including any processes, tasks, goals, and milestones.Doors Traceability & View Shows Gaps In Traceability Across Modules Sc 1 St IBM
5 Key Benefits of Using a Traceability Matrix to Stay on Top and in Control of Your Project
20 Critical Security Controls Spreadsheet —
attachment_e_requirements_traceability_matrix_2.xlsx Health Insurance Portability And
TEMPLATE 2019 Update Security Requirements Traceability Matrix (SRTM) ⋆ The Cyber Sentinel
Requirements Traceability Matrix Excel Template
Basic Requirements Traceability Matrix Template
Security Control Traceability Matrix Template by ClickUp™
Cybersecurity Risk Assessment Template for creating cybersecurity risk assessments
Security Requirements Traceability Matrix Template
Related Post: